Recently, I got a new niche product, LazyCat MicroServer. First, I would like to thank LazyCat CEO Andy Stewart for the coupon provided, as I am a loyal user of the OpenAI Translator created by yetone. 😂

Like some other guys, when I saw the introduction to LazyCat MicroServer for the first time, I thought, “Isn’t it just a NAS?” I already own a NAS, and after playing around with it for a while, I realized that it looks like a NAS, but it falls short of a NAS in terms of data and service stability. However, it far surpasses NAS in terms of performance and flexibility. LazyCat MicroServer and NAS are entirely different products in separate lanes.
LazyCat MicroServer ≠ NAS
Here is why I think LazyCat MicroServer falls short of a NAS regarding data and service stability.
- NAS natively supports RAID. LazyCat MicroServer does have two data disks equipped but is not RAID-supported. Although the real-time Btrfs backups via external drives could be a decent compromised solution for users without a NAS, as someone who already owns a NAS, I will definitely not migrate the significant data to LazyCat MicroServer.
- NAS mainly has dual network interface cards (NIC) that support a variety of configurations, and I usually use NIC bonding to ensure one network port failure is tolerated for uninterrupted communication. However, most NAS devices do not natively support WiFi, but LazyCat MicroServe does, so the wired connection + WiFi combination is an acceptable compromise.
Considering these, I will not replace my NAS with LazyCat MicroServer. Of course, this is also not its market positioning.
LazyCat MicroServer > NAS Data and Service Stability Requirements Excluded
LazyCat MicroServer has some that attract me:
- Its performance is way better than most traditional NASes, and the equivalent high-performance NASes are way more expensive. Due to my NAS’ limited performance, I have to hold some deployments. But now I can deploy them on LazyCat Server and migrate most of the applications from NAS to LazyCat MicroServer. My NAS will be more of a data backup tool and media center.
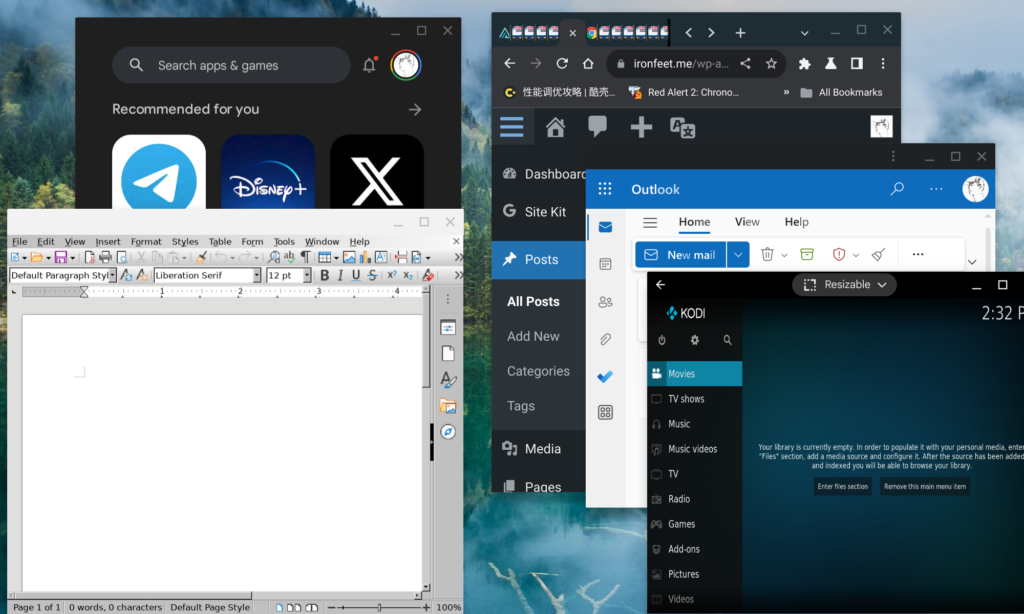
- The LazyCat AppStore is well-stocked, and the LazyCat MicroServer features configuration-free network tunneling. Its cross-platform SDK has quite an active community.
- LazyCat’s official apps have some features that Synology’s counterparts are incapable of. For example, leveraging its more powerful chipset and LLMs, the LazyCat Photo app supports natural language photo queries. The upcoming version will also support duplicate photo detection and cleanup. Synology Photos, in contrast, is lack of this functionality despite its predecessor, Moments, having it. The community has requested Synology to reinstate this feature for quite a long while, but no official response has been received. Moreover, Synology doesn’t offer an API for Synology Photos, making third-party solutions impossible. Before LazyCat, I had to rely on third-party tools to periodically scan my NAS for duplicate photo cleanup, which was very troublesome.
Unconventional Usage
In order to experience the exciting features of LazyCat official Apps without migrating significant data like photos to LazyCat MicroServer, I figured out an unconventional usage by using Syncthing.
Dual Usage of Synology Photos & LazyCat Photo App
First of all, I need to confirm whether this dual usage is feasible.
- I confirmed that the LazyCat Photo App supports both direct uploads from clients and files copied to its “Photos” directory.
- Syncthing supports folder filtering, which means we can exclude some unnecessary files or folders from syncing.
Next, I am going to set up based on the diagram below. 😂
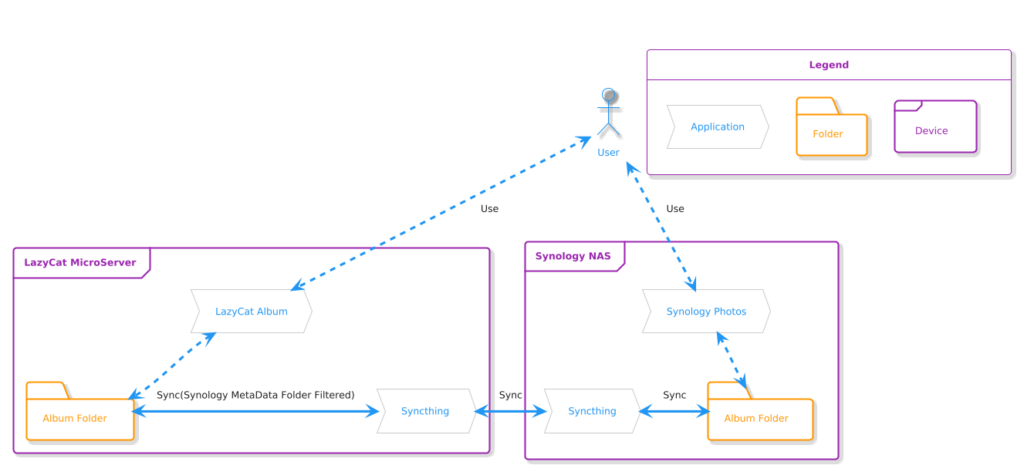
- I installed Syncthing on both my NAS and LazyCat MicroServer. The photo folder on my NAS syncs with a subfolder of the photo folder on LazyCat MicroServer. Additionally, I configured Syncthing to ignore Synology metadata directories,
@eaDir, on my NAS side. - I use Synology Photos’ mobile backup while keeping LazyCat’s backup disabled to avoid duplicate uploads.
In this way, I can manage my photos with the LazyCat MicroServer’s high performance while relying on my NAS to securely store cherished memories; All the changes made on either side sync to the other.
To Be Continued
I’m still exploring new ways to use the LazyCat MicroServer. For instance, I recently deployed a lightweight RAG (Retrieval-Augmented Generation) solution using AnythingLLM integrated with Ollama, and it was onboarded at LazyCat AppStore.
Admittedly, LazyCat MicroServer is not without any flaws: its SDK documentation is cryptic and incomplete, and the system, SDK, and website are riddled with bugs. The support team feels amateurish. The whole process of porting and developing applications on the MicroServer feels like pioneering uncharted territory. Despite its shortcomings, LazyCat’s rapid iteration, timely patches, and exceptionally quick support response give a strong impression of a product on the rise.
As the company’s first product of this kind, I have realistic expectations. Ironically, these imperfections make the process feel like an adventure, and I’m excited to keep exploring the MicroServer’s potential. Ironically, it’s the imperfections that make this journey engaging. The challenges add a layer of excitement, pushing me to dig deeper and explore more of the MicroServer’s potential. I’m eager to continue this adventure and uncover new possibilities.